Security you can trust
Eidoncore is built with defense-in-depth security at every layer — from encryption and authentication to tenant isolation and audit logging. Your agency data is protected by enterprise-grade controls.
Data protection at rest and in transit
All sensitive data is encrypted using industry-standard algorithms. Connections are secured with HTTPS/TLS at all times.
AES-256-GCM
Sensitive data encrypted at rest with HKDF key derivation
TLS 1.3 in Transit
All connections encrypted between browser and server
bcrypt Hashing
Passwords hashed with bcrypt cost-12 — never stored in plain text
HMAC-Signed Tokens
Password resets, invitations, and impersonation use tamper-proof signed tokens
Built-in protection against common threats
Security headers, rate limiting, and input sanitization protect your workspace from attacks.
Brute Force
Rate limiting on login, 2FA, password reset, and registration
XSS Prevention
CSP headers, server-side HTML sanitization, and React auto-escaping
CSRF Protection
Origin header validation and signed tokens on sensitive endpoints
HSTS Enforcement
Strict Transport Security with 1-year max-age and subdomain coverage
Clickjacking
X-Frame-Options DENY prevents embedding in iframes
DNS Verification
DNS-over-HTTPS verification for custom domain security
Loved by agencies
"As a healthcare-adjacent agency, data security is non-negotiable. Eidoncore's tenant isolation and encryption gave us the confidence to move forward."
Built for teams like yours
Enterprise Agencies
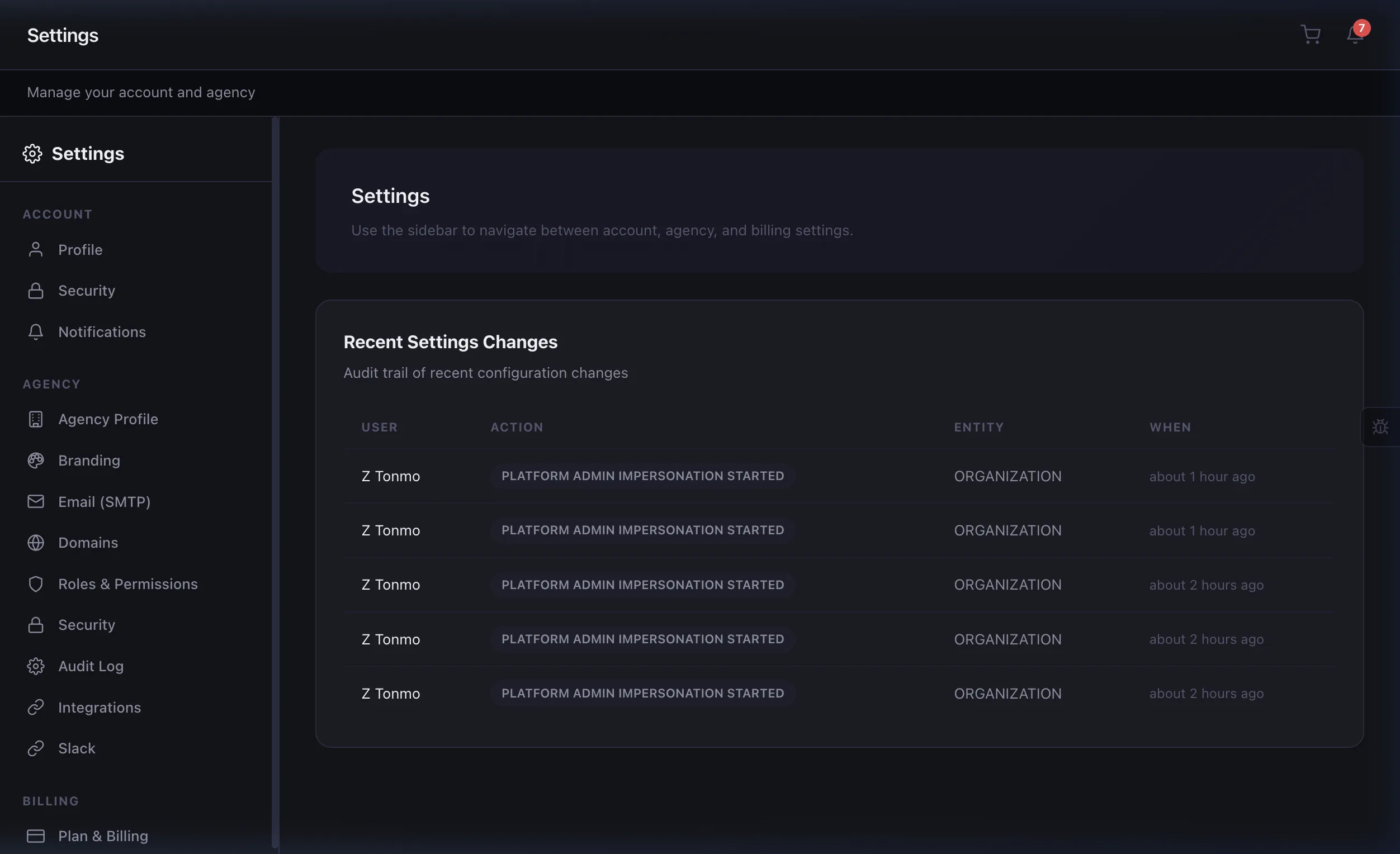
SOC 2 readiness, audit logs, and enforced 2FA across your organization.
Regulated Industries
AES-256 encryption, tenant isolation, and data residency options.
Client-Facing Teams
Prove your security posture to clients with enterprise-grade protections.
IT Administrators
Role-based access control, API key management, and session policies.
Frequently asked questions
Eidoncore is SOC 2 ready with enterprise-grade security controls including AES-256 encryption, complete tenant isolation, audit logging, and role-based access control.
Every agency operates in a fully isolated tenant. Database queries are scoped to the authenticated tenant, middleware enforces isolation, and cross-tenant access is architecturally impossible.
Yes. TOTP-based two-factor authentication is available for all accounts. Enterprise users can enforce 2FA for all team members as a security policy.
Eidoncore runs on enterprise-grade cloud infrastructure with data encrypted at rest (AES-256) and in transit (TLS 1.3). Regional deployment options are available for Enterprise customers.
Related features
Your data deserves enterprise-grade protection
Start your 14-day free trial with full security features from day one.